To create your validated and signed SSL certificate, but by a trusted CA – Certificate authority. we will need to:
1- Generate then pass your CSR – Certificate Signing Request – file to the CA.
2- Get the output certificates from the CA, then create a bundle PEM file, or use each output separately.
To generate the csr file run the commands.
# openssl genrsa -out domain.com.key 2048
# openssl req -new -sha256 -key domain.com.key -out domain.com.csr
the output will be as shown below but remember to leave the challenge password blank.
You are about to be asked to enter information that will be incorporated into your certificate request. What you are about to enter is what is called a Distinguished Name or a DN. There are quite a few fields but you can leave some blank For some fields there will be a default value, If you enter '.', the field will be left blank. ----- Country Name (2 letter code) [XX]:US State or Province Name (full name) []:Wyoming Locality Name (eg, city) [Default City]:Sheridan Organization Name (eg, company) [Default Company Ltd]:CompanyName Organizational Unit Name (eg, section) []:IT Common Name (eg, your name or your server's hostname) []:domain.com Email Address []:email@domain.com Please enter the following 'extra' attributes to be sent with your certificate request A challenge password []:Leave blank An optional company name []:Leave blank
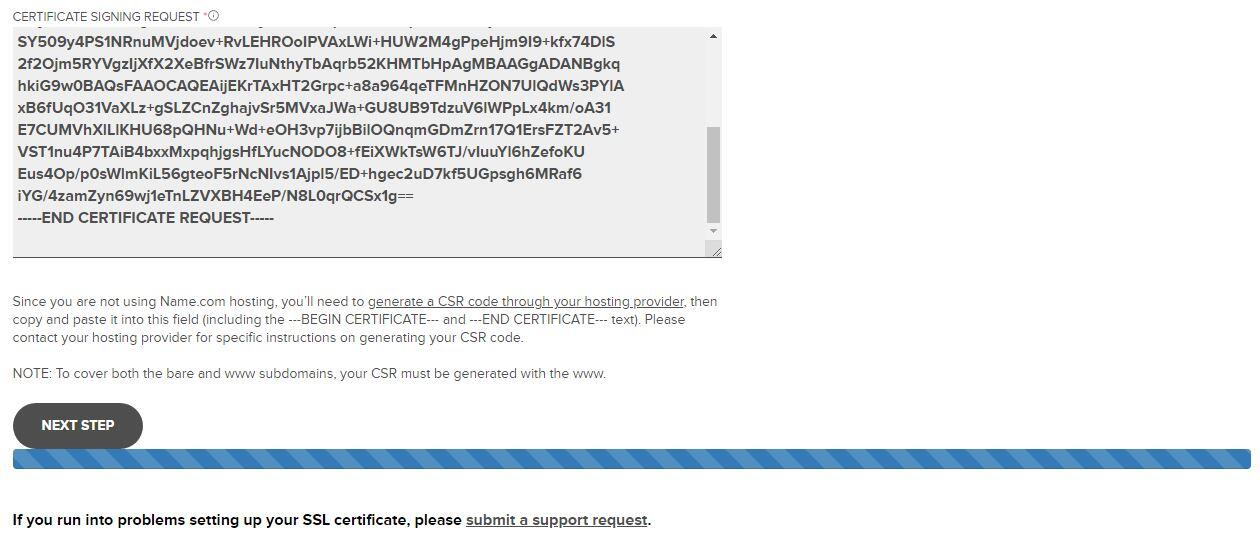
Then pass the output CSR file to the CA, or the CA partner as shown below for the name.com using RapidSSL
If your SSL certificate has been issued successfully, CA or partner will reply to you with: SERVER CERTIFICATE, CA CERTIFICATE (INTERMEDIATE), and ROOT CERTIFICATEs.
now create a domain.com.bundle.crt file and copy/paste to combine the above 3 certificate code in the same order into a bundle file.
# vim domain.com.bundle.crt
For hardening this SSL Certificate we will generate Diffie-Hellman group dhparam.pem file
# openssl dhparam -out dhparam.pem 4096
So you can use the output files into webserver as nginx for an example
.................... .................... ssl on; .................... ssl_certificate /path/to/domain.bundle.crt; ssl_certificate_key /path/to/domain.com.key; ssl_dhparam /path/to/dhparam.pem; ...................



